Flaw in gay app Jack’d makes users’ private nudes public

(Pexels)
Gay dating and hook-up app Jack’d has accidentally exposed users’ private photos.
The flaw has been in effect for three months and can be exploited by anyone with a web browser who knows it exists, British technology news site The Register reported on Tuesday (February 5).
There is no need for hackers to prove their credentials or even sign up for the app, which gay, bisexual and queer men use to talk, swap private photos and arrange meet-ups.
Jack’d says the app has five million users in countries around the world.
“Our tech team is aware of the photo vulnerability and has already programmed the changes for this fix.”
— Mark Girolamo, chief executive of Jack’d parent company Online Buddies
Users who may not be out to their friends, family or community risk having their sexuality exposed, while the flaw also puts users at risk of bullying, abuse or blackmail.
Jack’d users who live in any of the several dozen countries where homosexuality is not legal may also be adversely affected by the security flaw.
Gay app Jack’d responds to news of security flaw
Mark Girolamo, chief executive of Jack’d parent company Online Buddies, told PinkNews: “Our tech team is aware of the photo vulnerability and has already programmed the changes for this fix.
“They will deploy the fix this Thursday, February 7.”
The company did not respond to questions about why the issue has not been fixed in the three months since Jack’d was reportedly made aware of the flaw.
Before Jack’d, Grindr faced criticism over leaks
In September, a mistake allowing people to generate maps of people’s precise locations on Grindr was exposed.
Queer Europe posted an exposé of the app’s flaws, revealing that freely available third-party tools have been created to take advantage of Grindr’s vulnerabilities.
Although Grindr usually only shows the distance between two users who have locations switched on, it was possible for rogue users to take measurements from different locations and triangulate the location of other people on the app.
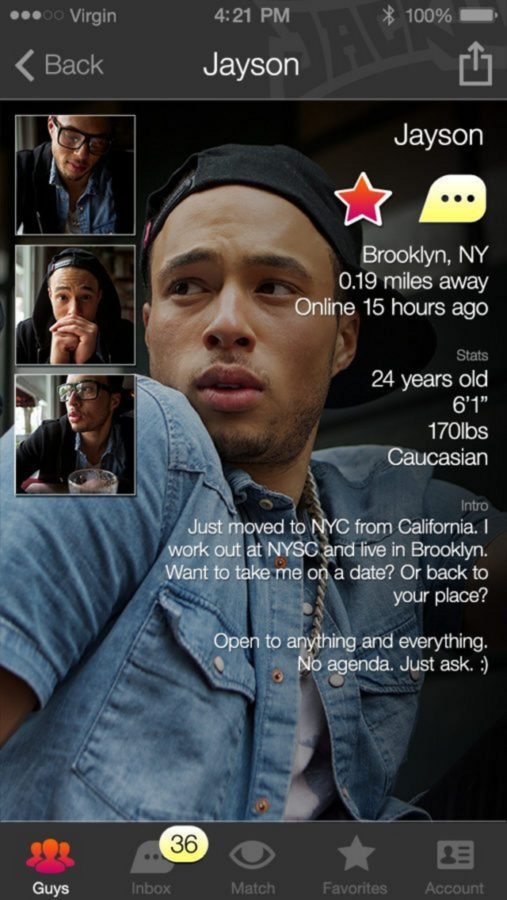
Jack’d provides millions of users with the opportunity to chat, meet and swap photos. (Jack’d)
The tool also pulled data from users’ profiles on the app, including people’s names, preferred sexual positions, HIV status and profile photos.
In April 2018 it was reported that data on users’ HIV statuses was being disclosed to two private companies that help “optimise” apps, Localytics and Apptimize.
Norwegian research group SINTEF also alleged that Grindr was sending companies data about users’ sexuality, relationship status, ethnicity, phone ID, and even their sexual identity tribe—such as “twink” or “daddy.”
After intense backlash, Grindr said it would stop giving away the information, which it emphasised had not been shared for commercial reasons.